Possibilities of complex problems are inherent in IT devices. Any damage or potential data loss regarding business processes of corporate systems, or the access to their confidential data by unauthorised parties may entail significant loss of prestige and material damage. Our surveillance services were specifically established by focus on the avoidance of such risks.
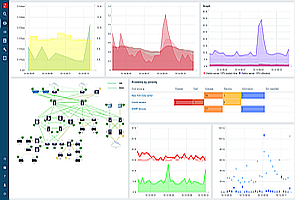
 For all companies, the maintenance of records about their business processes and continuous availability of data are especially important. Therefore, when establishing the IT system of a well-functioning company, the availability and operational security of the system surveyed, as well as its recoverability in the event of errors are managed as tasks of high priority by us. Statistics and data that can also be used in practice are equally important, and they are relevant from a professional aspect to both operators and users. By the analysis of data we may obtain a more accurate picture on the operation of servers and network devices, and the use of IT services.
For all companies, the maintenance of records about their business processes and continuous availability of data are especially important. Therefore, when establishing the IT system of a well-functioning company, the availability and operational security of the system surveyed, as well as its recoverability in the event of errors are managed as tasks of high priority by us. Statistics and data that can also be used in practice are equally important, and they are relevant from a professional aspect to both operators and users. By the analysis of data we may obtain a more accurate picture on the operation of servers and network devices, and the use of IT services. By the use of data and system messages created in the course of surveillance monitoring, operations will be made simpler and more secure. By the use of the available data we can quickly and efficiently intervene in the case of fault prevention and troubleshooting. By ongoing surveillance and control of the system, hidden errors and deficiencies will be revealed.
By the use of data and system messages created in the course of surveillance monitoring, operations will be made simpler and more secure. By the use of the available data we can quickly and efficiently intervene in the case of fault prevention and troubleshooting. By ongoing surveillance and control of the system, hidden errors and deficiencies will be revealed.By our IT surveillance service, we provide solutions to all the requirements and problems mentioned above. Our surveillance system supplies our customers by automated, event controlled information, and in the case of using our IT operational services, we are able to commence troubleshooting immediately.
Systems supported by our surveillance service
- Monitoring of server hardware components.
- Monitoring of server operations systems and the services thereof.
- Monitoring of server applications.
- Monitoring of firewalls and firewall services.
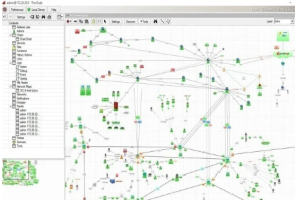
- Monitoring of network devices and the services thereof.
- Monitoring of connections of network systems and the sites thereof.
MONITORING TOOLS:
- Zabbix monitoring system
- Mikrotik Dude monitoring